Trojans might open ports on user PCs to convey data invisibly, and sniffers may scan your network connection for flaws that could be exploited. Despite major advancements in antivirus and malware technology throughout that time, the finest firewall services remain a recommended prerequisite for all PC users, as hazards have changed rather than disappeared totally.
While any competent antivirus application can protect your computer from obvious criminal activity, software, and apps can sometimes abuse their permissions to generate unauthorized network connections that can be used to harvest user data.
That’s why we have come up with a list of the Best Free Firewall Software for your protection. Your best chance of keeping your equipment malware-free is to install antivirus software as well as an additional firewall. Thankfully, you don’t have to spend a fortune or even pay a penny for third-party software.
Table of Contents
What is a Firewall?
A firewall is a shield or barrier that secures devices linked to the internet or another network, such as a local area network (LAN), against illegal access. A firewall on a PC, phone, or tablet protects users from data-based malware risks found on the internet and other linked networks.
Data passes between your PC and servers and routers in cyberspace. A firewall monitors the data, which is sent in packets, to identify and stop any undesirable traffic. The firewall achieves this by comparing data packets to the rules that have been established. The data packets are acknowledged by the firewalls if they comply with these rules. If they don’t follow the rules, the firewall will reject or block them.
Let’s dive into the list of Best Free Firewall Software-
1. ZoneAlarm
For more than 20 years, ZoneAlarm has been one of the most popular firewall solutions, with over 20 million downloads. ZoneAlarm is available in both a free and a paid edition. The former is ad-supported and lacks several features such as expert rules, 24/7 assistance, component control, and other advanced options.
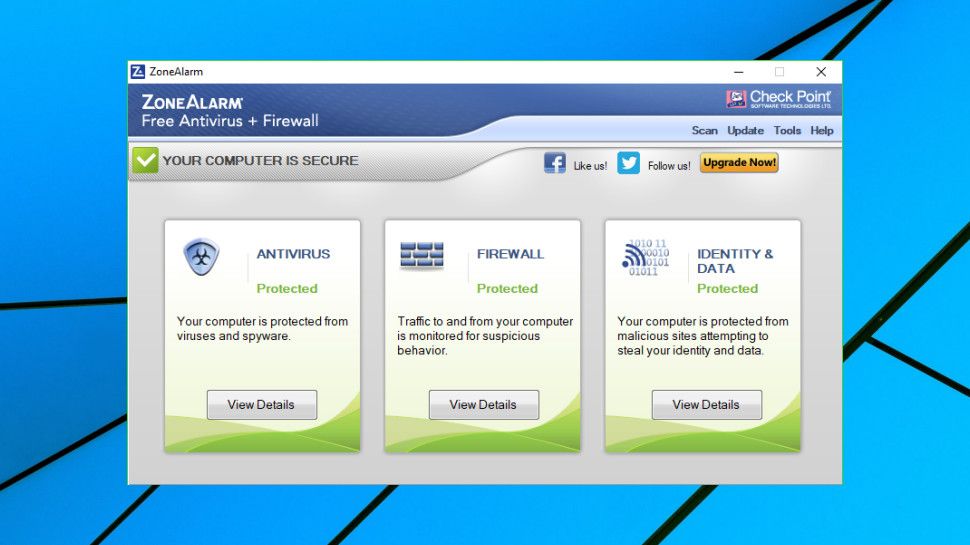
It also has a two-way firewall that monitors traffic entering and exiting your network, hides your PC from hackers, and prevents spyware from broadcasting your personal information. Additionally, early boot protection will keep your computer from being booted from a harmful rootkit that is attempting to take control of your computer.
ZoneAlarm now offers URL scanning for anti-phishing to ensure you don’t enter personal information on websites that have been flagged as security concerns. It will also clean any files you download of malicious code.
2. GlassWire
GlassWire is one of the most visually appealing free firewalls on the market. You’ll be able to examine your present and previous network activities, making it simple to spot dangers to your computer, thanks to its attractive interface.
GlassWire will also notify you if your PC or programs have changed as a result of your Internet usage. It will also keep an eye on your network and notify you if any strange devices attempt to connect.
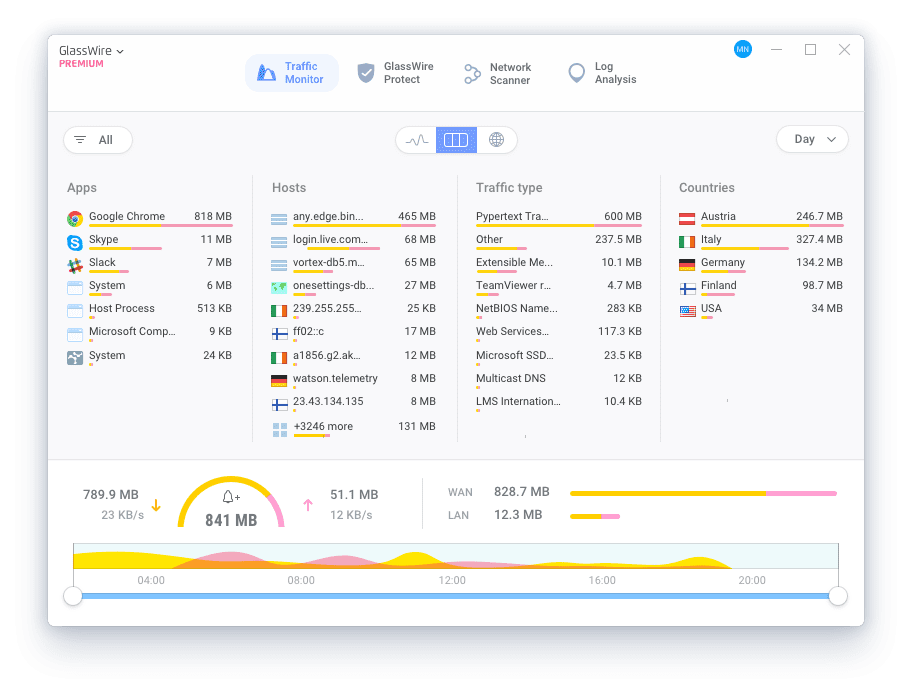
The showing of detailed network consumption statistics split down by IP/Host, application, and kind of network traffic is probably its best feature.
To accept or refuse new app connections, GlassWire offers an ‘Ask to Connect’ mode. And if you ever feel overwhelmed by the amount of data available, you can clean the logs in a matter of seconds to return them to a more manageable condition.
Also Read: 8 Best Photo Editing Apps for iPhone
3. AVS Firewall
This firewall is compatible with all Windows versions, from XP to Windows 10. The AVS Firewall protects you while you’re surfing and keeps your PC safe.
An ad and pop-up blocker, as well as parental settings, are among these safeguards. Devices, applications, and programs can all have bandwidth use limitations set.
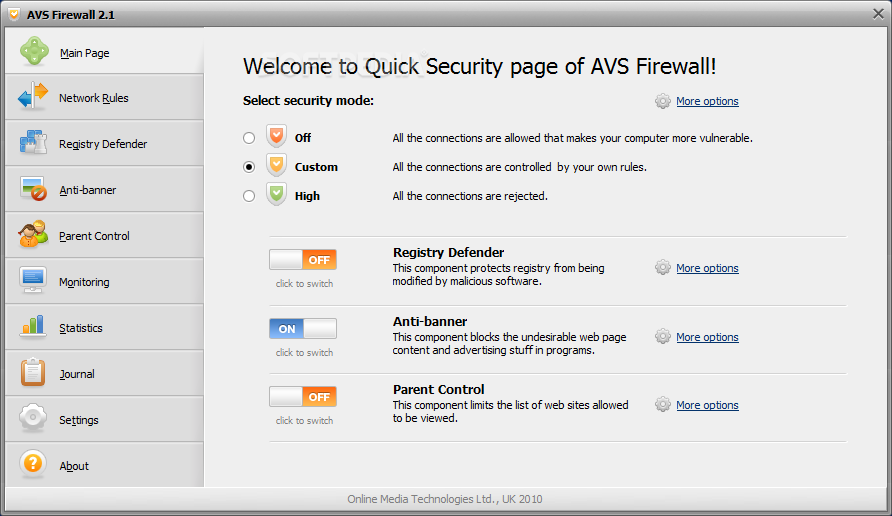
Incoming connection requests will be blocked, and other security measures will be implemented. These features include the ability to choose which applications on your computer are permitted to connect to the internet, as well as a security level function. The software keeps track of what’s going on in the registry and prevents changes. This is a critical safeguard against worms and other persistent infections.
4. Comodo Firewall
Comodo Firewall provides a hefty dish of features for a free product. It will verify the legitimacy of every incoming and outgoing traffic, hide your computer’s ports from hackers, and prevent rogue applications from broadcasting your personal information.
It will alert you quickly if there is any questionable behavior. The Comodo browsers include security, privacy, and performance features not found in other browsers.
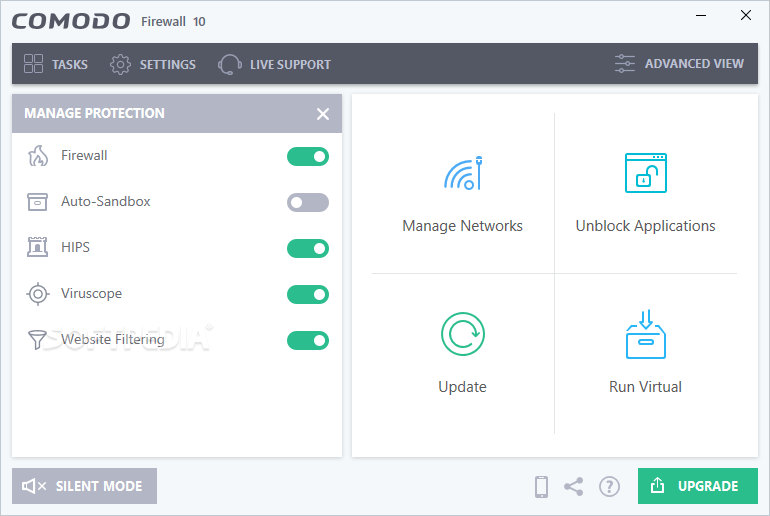
A secure browser, a ‘virtual kiosk,’ and a host intrusion security system are also included (HIPS). When a program exhibits questionable activity, the HIPS will prompt you to approve, block, or treat the program as an installation. Comodo also has its own more secure versions of Chrome and Firefox, known as Dragon and IceDragon, respectively.
Also Read: 12 Best GarageBand Alternatives for Android in 2021
5. TinyWall
TinyWall is designed to work in conjunction with Windows’ built-in Defender firewall, so it has a low-performance impact. TinyWall will actively block trojans, viruses, worms, and other forms of malware, as well as dangerous programs from changing the settings of the Windows firewall. And it’ll do it all without you having to know anything about ports, protocols, or application specifics.
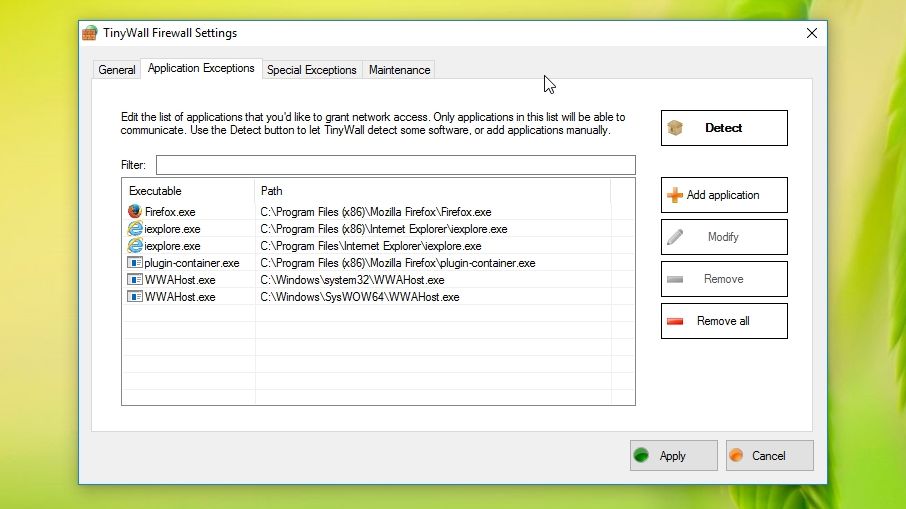
But its no-popup method is undoubtedly the most enticing feature. When an application tries to access the Internet, most firewalls will display a pop-up asking you what you wish to do. Not only is this inconvenient, but to get rid of the popups, you’ll have to grant access to everything, which isn’t very secure.
TinyWall circumvents this issue by requiring you to whitelist programs that you want to be allowed to access the Internet.
Businesses deploy firewalls regularly to safeguard their resources from assault, but the general public has lost interest in this type of security. Protection is frequently included in equipment, which contributes to this complacency. With the introduction of Trojans, this incoming connection request block is no longer sufficient; Trojans will open up outgoing connections back to base, allowing more viruses to infiltrate.
Also Checkout: How To Share Files From Android To iPhone Immediately




